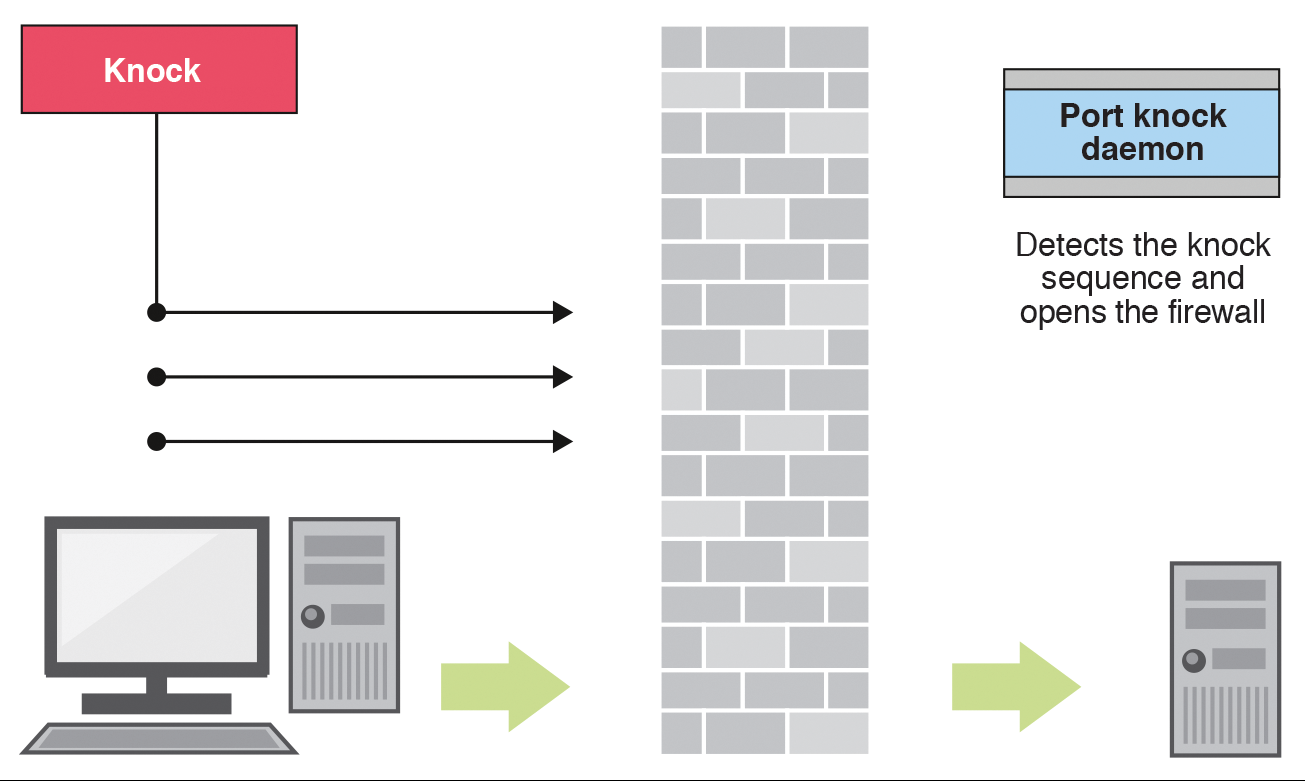
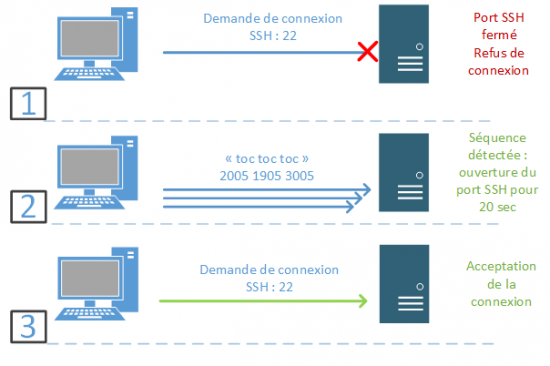
Port knocking example. The firewall is opened in response to a specific... | Download Scientific Diagram

Port knocking example. The firewall is opened in response to a specific... | Download Scientific Diagram
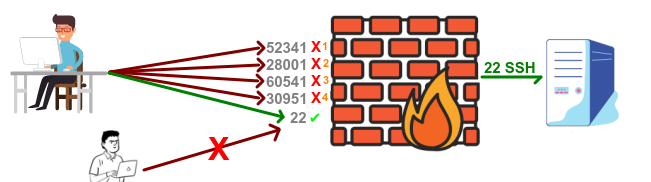
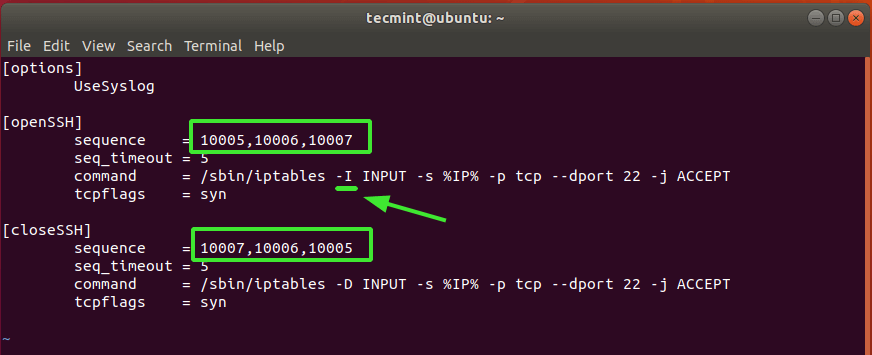
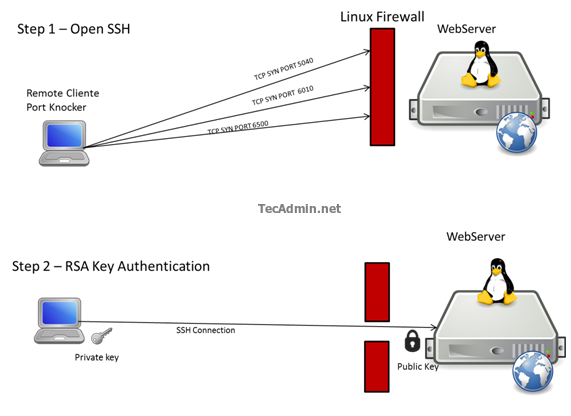
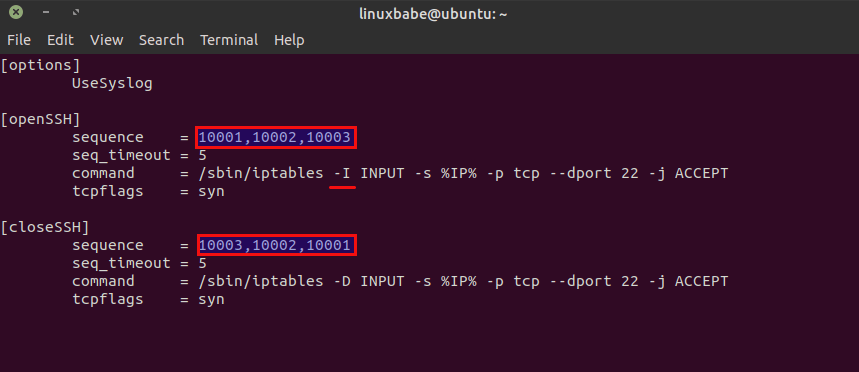
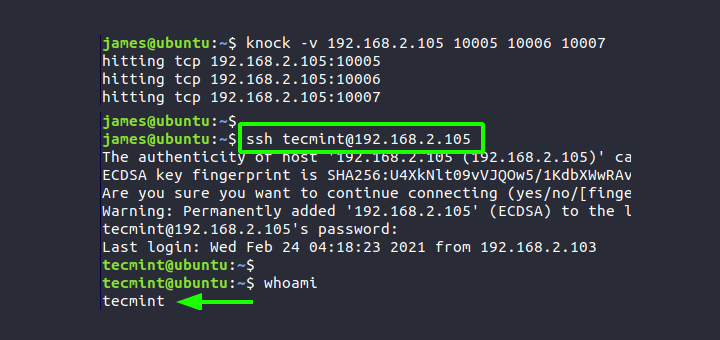
Port knocking, aprenda a melhorar as política de segurança de seu firewall Linux e Mikrotik - Remontti



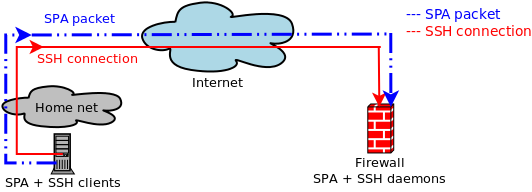




![minipost] Mikrotik/RouterBoard port-knocking example for firewall/NAT openings – NetworkGeekStuff minipost] Mikrotik/RouterBoard port-knocking example for firewall/NAT openings – NetworkGeekStuff](http://networkgeekstuff.com/wp-content/uploads/2014/06/Mikrotik_port_knocking.png)